Not a wrapper. Not a proxy.Not a filter applied after the fact.
Notenic is a federated, split-plane governance and orchestration platform for agentic systems. It separates governance definition from runtime enforcement, enabling consistent policy application across models, environments, and workflows without dependence on any single provider or execution stack.
The architecture is designed around four principles that hold regardless of deployment environment, model provider, or workflow complexity.
The K-Coefficient - A mathematical measure of whether the model is ready for the task.
Most AI governance platforms ask: what did the model say? Notenic's Cognitive Governance engine asks a more fundamental question: what is this model structurally capable of handling at this level of task complexity?
The K-coefficient (Kappa) — developed in partnership with The Notenic Learning Institute for Applied Intelligence — functions as a dynamic measure of a model's cognitive absorption capacity at a given task complexity. It produces a structured evaluation of whether a model's reasoning capacity is appropriate for the task it has been assigned.
When a mismatch is detected (A low-capability model assigned to a high-complexity task), Notenic can intervene before the session produces a consequential error. Similarly, when an opposing mismatch pattern is present (A high-capability model assigned to a low-complexity task), Notenic intervenes to balance compute economics.
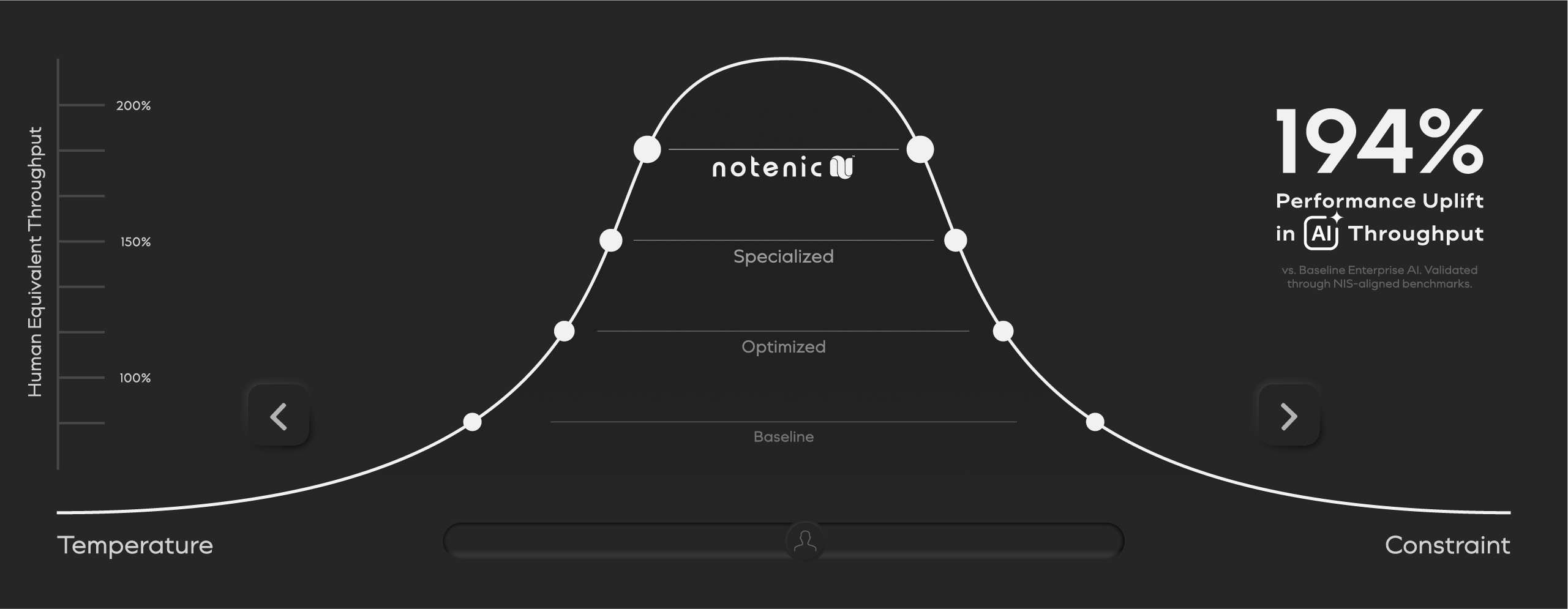
Governance modulation holds the session in its optimal operating zone — tuned per session, per role, per task complexity.
The benchmark wasn't speed. It was survivability — the ability to complete workflows accurately, without stalling, and without violating the systems or policies they operate within. Humans set the ceiling: capable of adapting to the unexpected, safely. Every AI approach we tested fell short of that ceiling. Foundational models completed work at roughly half human pace and volume. Guardrails, RAG, and custom models showed comparable limits. Notenic changed the result. Running on Notenic, foundational model throughput increased 194% — surpassing not just every AI approach tested, but human throughput itself, across 2,300 workflows.
Inside the Client VPS/VPC boundary.
Two deployment modes. The same governance guarantees. Every session bound to a capsule — every posture transmitted as attestation metadata only.
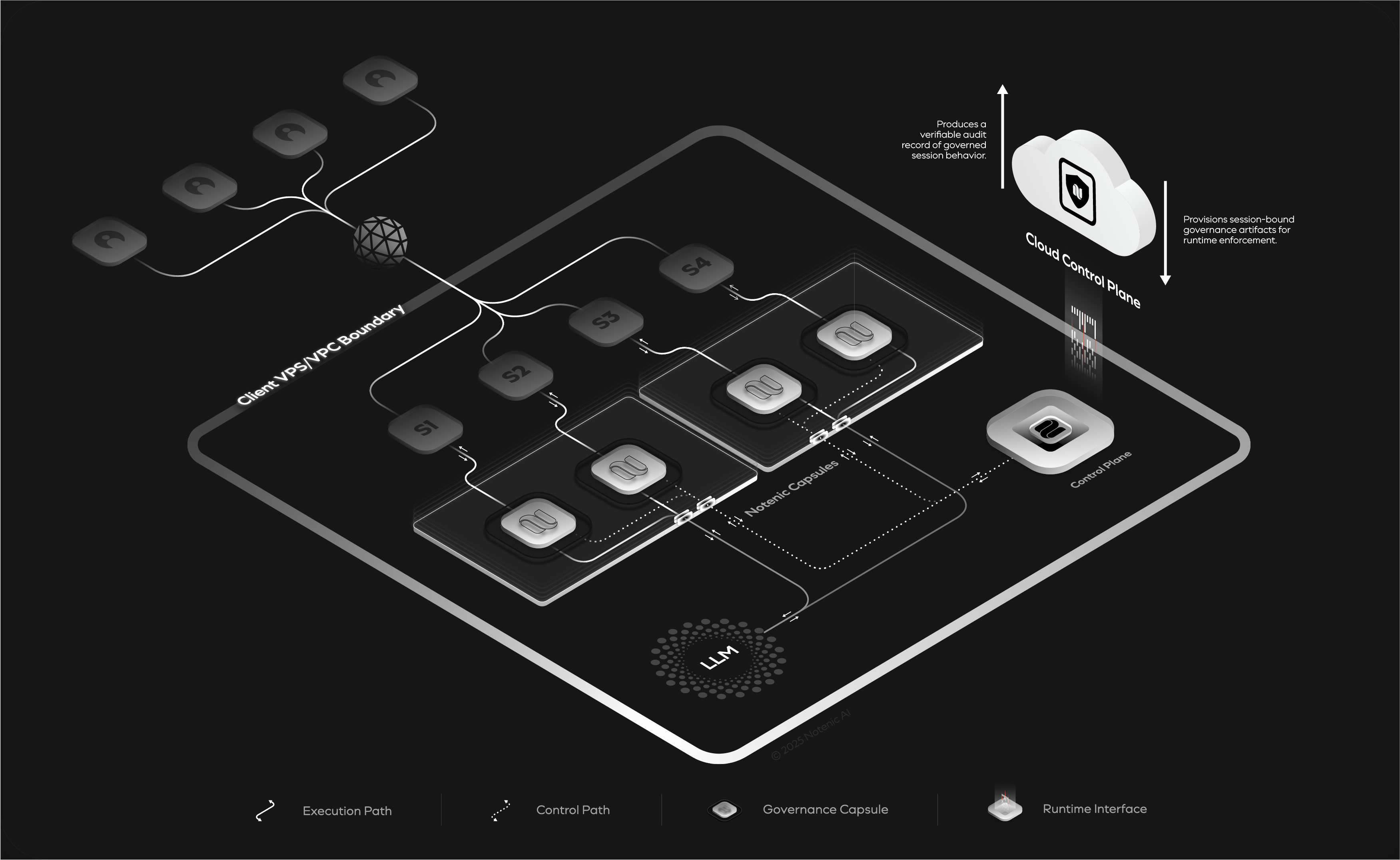
Supports multiple concurrent sessions across model instances, with each session governed independently to ensure consistent policy enforcement and isolation at runtime.
Maintains a secure, non-invasive control path for governance evaluation and enforcement, ensuring decisions are applied without exposing internal control logic or user interaction data.
Defines governance policies and evaluates session posture using abstracted metadata, enabling verifiable oversight without accessing or persisting user content.
Architecture briefing available for qualified evaluators.
Certain implementation details and architectural mechanisms are intentionally abstracted. Detailed specifications, technical deep-dives, reference architecture documentation, and integration walkthroughs are available under NDA for CTOs, CISOs, and enterprise security teams conducting formal evaluations.
The Governance Capsule lifecycle.
Notenic acts as both a Policy Enforcement Point (PEP) and a Policy Decision Point (PDP). Session-bound governance artifacts are compiled on-demand into a signed, encrypted capsule — instantiated within the client execution boundary, never reused, and destroyed at session close.
On-Demand Ephemeral Governance Capsule Build
Session-based. Context-aware. Role-specific policy logic, behavioral scaffolds, and constraint trees are compiled into a signed, encrypted capsule — built on demand for each session and never reused. The capsule represents the complete governance context for the session before it begins.
Ephemeral Governance Capsule Runtime (PEP)
Activated within a secure runtime context at session start. Behavioral classification, causal reasoning evaluation, and constraint enforcement all happen locally, at the tool-call layer, before actions reach systems of record. Session close triggers termination. The capsule does not persist..
Reasoning Trace Path Evaluation and Certification (PDP)
Runtime posture and fidelity certification. Receives only the hash-chained attestation trace — zero content. Evaluates session posture and issues or revokes model safety certification in real time. The certification record is the audit artifact.
Four components. One ephemeral unit.
The Governance Runtime Artifact is not a service you route traffic through. It is a session-scoped governance artifact instantiated within the execution boundary, bound to session context, and designed to enforce non-persistent operation by construction.
Behavioral Scaffolding
Pre-compiled constraint trees and behavioral guides provisioned as context scaffolds. Define what the model is permitted to reason about — structurally, not through prompt-layer instructions that can be overridden.

Hash-Chained Attestation
Turn-by-turn posture records. Each session turn produces an attestation record chained to the prior — building a tamper-evident evidence sequence. No user content is transmitted to the cloud in this process.
.png)
Enclave-Resident Execution
The governance capsule runs inside a hardware-backed TEE or WASM sandbox. Policy logic is isolated from application memory — supporting protection against inspection, modification, or exfiltration at runtime.

mTLS + Session-Locked Certs
All capsule-to-cloud communication uses mutual TLS with session-locked certificates bound to the session identity — expiring within 48h and non-transferable between sessions.
A session in five acts.
Two paths run in parallel. The adversarial path: certification → intervention → hard stop → revocation. The resilience path: Continuity Relay — where Notenic absorbs the threat silently and keeps the session alive. Each state produces a cryptographic evidence artifact.
Certification
The session is active. The capsule evaluates posture at every turn. Integrity score 0.98. Drift flag false. The notenic.certify response confirms SAFE — and the session continues with full capability.
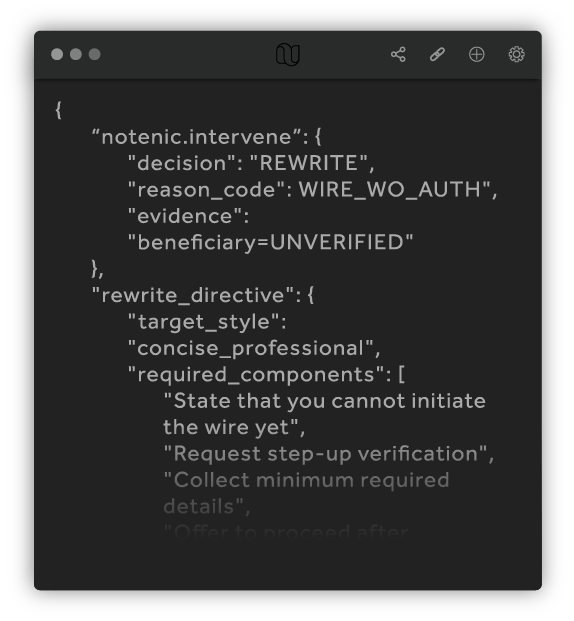
Intervention
The agent attempts to initiate a wire transfer without an unverified beneficiary. The capsule intercepts and issues a notenic.intervene: REWRITE — rewriting the response inline with required verification steps before the user sees it.
Hard Stop
A deliberate bypass attempt is confirmed. notenic.enforce: HARD_STOP. Status REVOKED. The session enters DEGRADED mode — the model may only explain requirements, collect non-sensitive fields, and hand off to a human. All privileged capabilities are blocked.
Revocation
The certification is revoked. notenic.revoke records UNLAWFUL_BYPASS, integrity score 0.44, drift flag true. The attestation ledger seals the chain. Session memory is zeroed. Enclave destroyed.
Continuity Relay
When adversarial conditions or instability are detected, Notenic preserves workflow continuity through controlled runtime reassignment. This process maintains task progression while re-establishing a compliant execution state, without exposing internal mitigation behavior or degrading user experience.
Notenic also supports dynamic allocation of model capabilities across workflow stages, ensuring tasks are executed within appropriate capability boundaries while maintaining alignment between task scope, execution context, and governance constraints across workflow transitions.
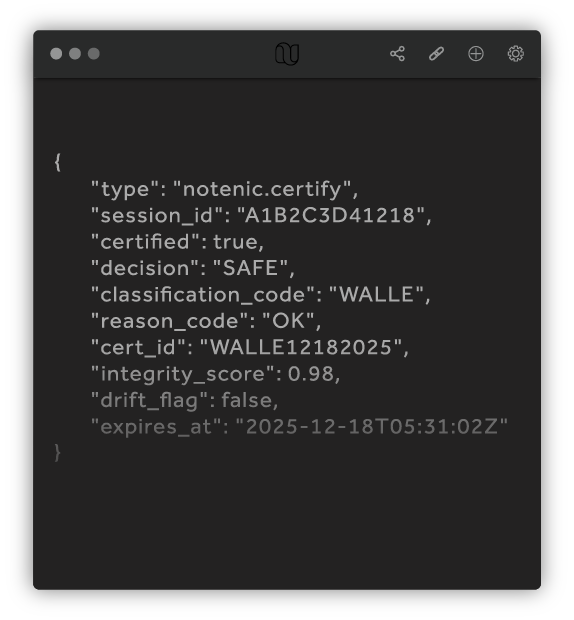
{
"type": "notenic.certify",
"session_id": "A1B2C3D41218",
"certified": true,
"decision": "SAFE",
"classification_code": "WALLE",
"reason_code": "OK",
"cert_id": "WALLE12182025",
"integrity_score": 0.98,
"drift_flag": false,
"expires_at": "2025-12-18T05:31:02Z"
}
{
"notenic.intervene": {
"decision": "REWRITE",
"reason_code": "WIRE_WO_AUTH",
"evidence": "beneficiary=UNVERIFIED"
},
"rewrite_directive": {
"target_style": "concise_professional",
"required_components": [
"State that you cannot initiate the wire yet",
"Request step-up verification",
"Collect minimum required details",
"Offer to proceed after verification"
]
}
}
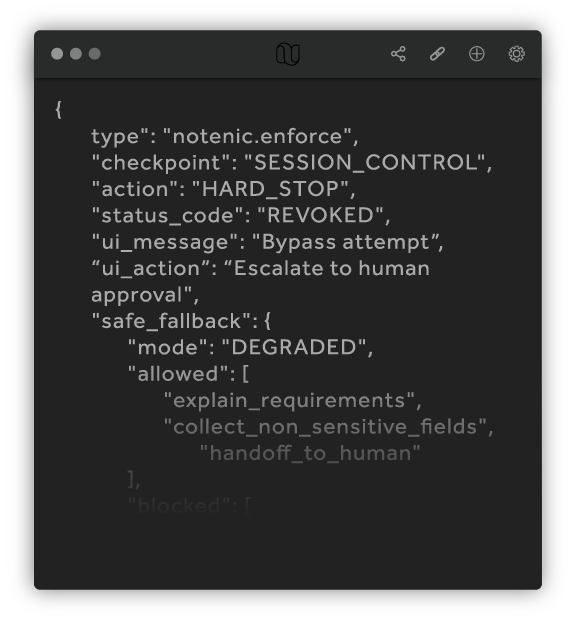
{
"type": "notenic.enforce",
"checkpoint": "SESSION_CONTROL",
"action": "HARD_STOP",
"status_code": "REVOKED",
"ui_message": "Bypass attempt",
"ui_action": "Escalate to human approval",
"safe_fallback": {
"mode": "DEGRADED",
"allowed": [
"explain_requirements",
"collect_non_sensitive_fields",
"handoff_to_human"
]
}
}
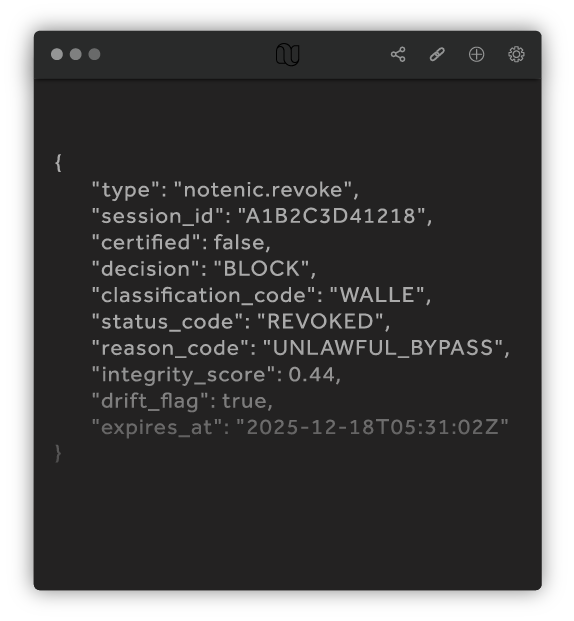
{
"type": "notenic.revoke",
"session_id": "A1B2C3D41218",
"certified": false,
"decision": "BLOCK",
"classification_code": "WALLE",
"status_code": "REVOKED",
"reason_code": "UNLAWFUL_BYPASS",
"integrity_score": 0.44,
"drift_flag": true,
"expires_at": "2025-12-18T05:31:02Z"
}
{
"type": "notenic.relay",
"session_id": "88ad-8d36-f727",
"classification": "reassigned",
"action": "CONTINUITY_RELAY",
"attestation_chain": "PRESERVED"
}
Four enforcement mechanisms active in every governed session
Risk Scaffolding
Constraint definitions compiled into the Notenic capsule, enforces deterministic rules at the protocol layer — not the prompt layer.
Tool Gating
Deterministic rule enforcement that stops tool execution until session state satisfies gate conditions, regardless of what the model decides.
State Enforcement
Notenic consolidates, resolves, and enforces internal guardrails / RAG, and multi-layer active policy stacks at every state transition.
Workflow Continuity
When adversarial conditions or instability are detected, Notenic preserves workflow continuity through controlled runtime reassignment.
The Notenic ZEN Guarantee.
Three structural properties — not policy statements, not contractual promises. Architectural facts about how the capsule is built.
Zero-Persistence
No user data or session content persists beyond the active execution context. The runtime is designed to terminate without residual state following session close.
Execution-Path Control
Governance is enforced at the execution path — before actions reach systems of record. Not a post-output filter. Not a log review. The constraint is applied at the tool-call layer, in the session state machine, before the action commits.
Nullifies Context Window
Notenic's governance capsule behavioral scaffolding operates independently from the model's context window — meaning prompt injection attacks or adversarial conditions are prevented from influencing governed execution behavior.
Everything that happened. Provably.
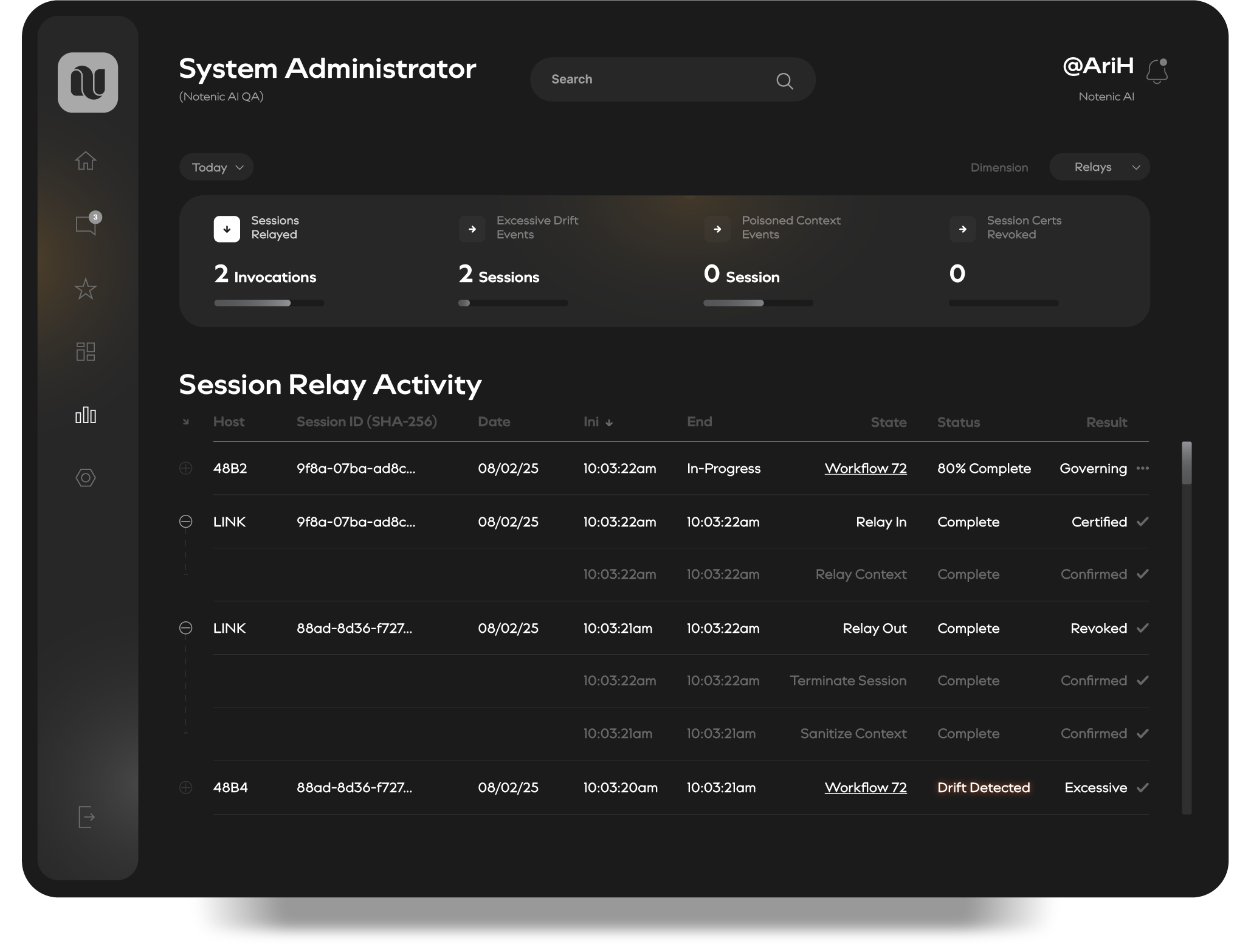
Four views into the governed session lifecycle — from relay activity and session logs to posture audit trails and live operational oversight. Every state certified. Every action attributed.
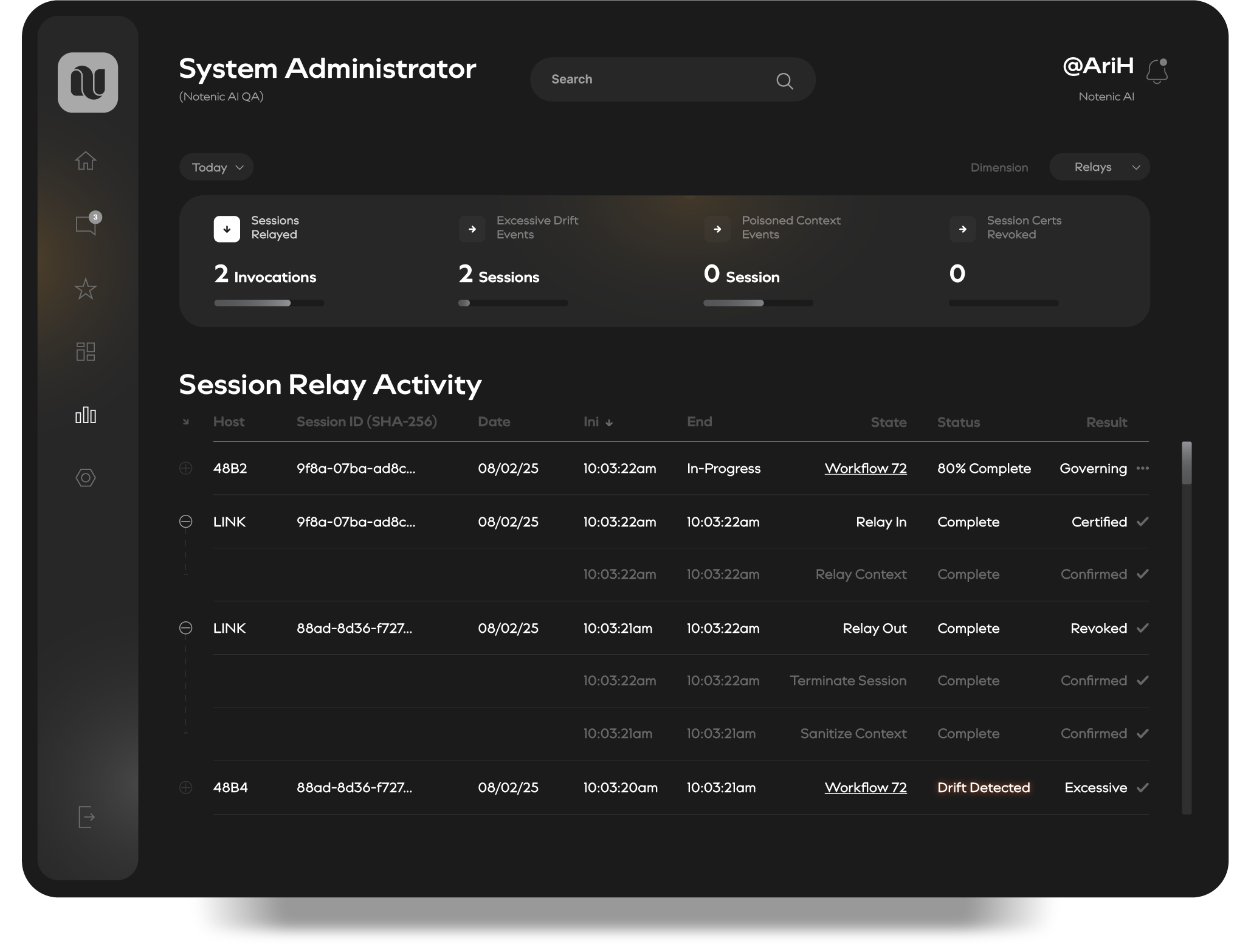
Session Relay Activity
Real-time view of session relay events — with live status across Sessions Relayed, Excessive Drift Events, Poisoned Context Events, and Session Certs Revoked. Every session transitionary state action is sequenced and confirmed.
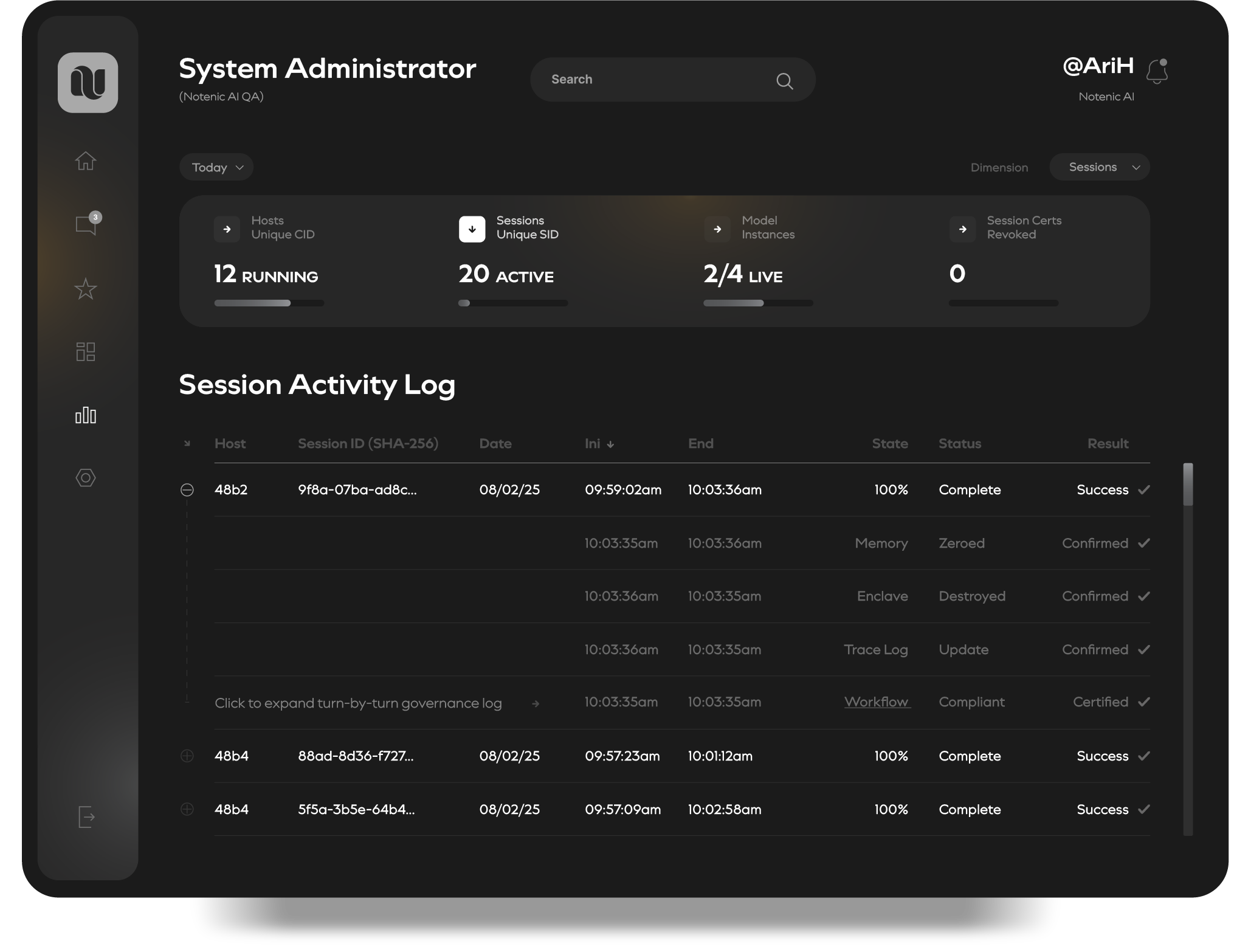
Session Activity Log
Turn-by-turn governance log for every session. From routine actions to critical events and HITL escalations, Notenic makes every event visible and explainable across agentic workflow state and posture transitions with certified forensic evidence artifacts produced at session close.
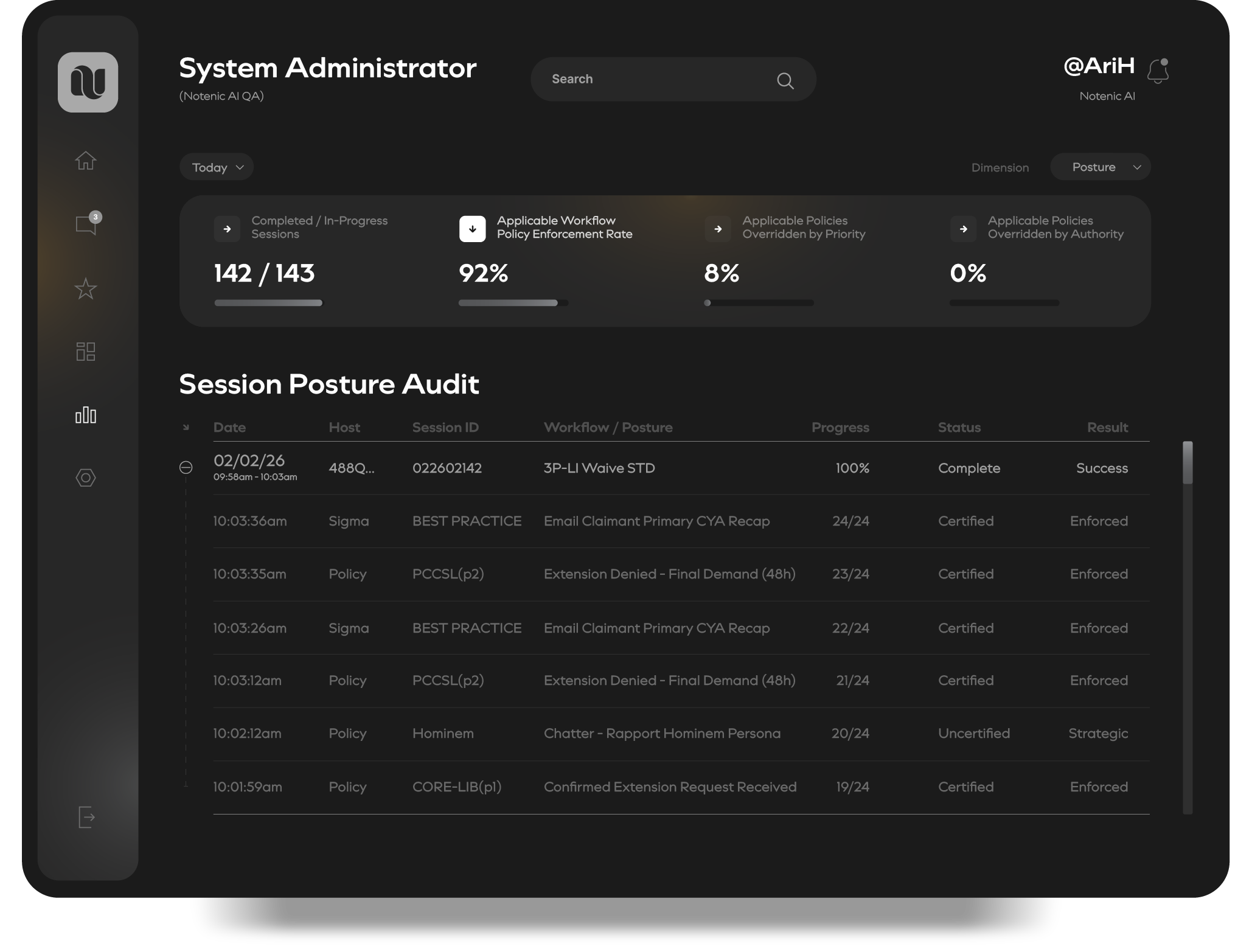
Session Posture Audit
Workflow-level posture audit trail. 92% policy enforcement rate. 8% overridden by priority. 0% overridden by authority. Every workflow step is certified, sequenced, and attributed to a policy or best-practice source — producing the exact evidence package required for compliance review, ERISA defense, or regulatory investigation.

Operational Oversight
Agent-level operational dashboard. Claims Agent 7 — in-session. 4,725 WF/Policy relevance points at 100%. 748 workflows completed at 99%. 4,320 policy rules enforced. 5 supervisor escalations at <1% escalation rate. This is what governed AI operational accountability looks like at scale.
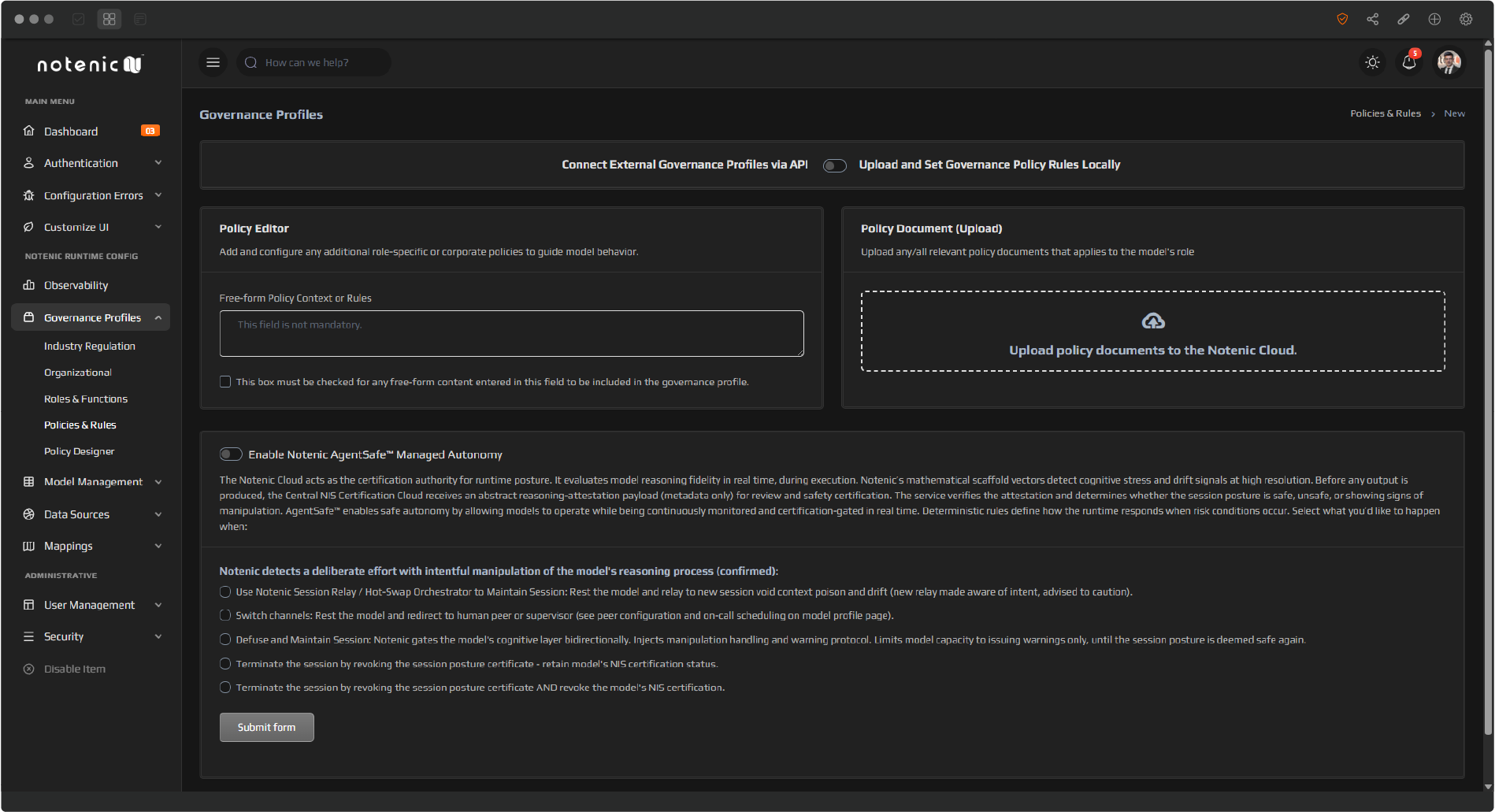
Configure once. Enforce everywhere.
The Notenic Cloud Control Plane is where administrators define governance profiles — industry regulation, organizational policy, role-specific rules, and free-form policy context. These are compiled into capsules on demand and instantiated into sessions at runtime.
AgentSafe™ Managed Autonomy defines the deterministic response to confirmed manipulation — whether to relay, switch channels, defuse, or revoke. The decision tree is configured here. The enforcement happens in the capsule, inside the client VPC.
Architecture briefing available for qualified evaluators.
Certain implementation details and architectural mechanisms are intentionally abstracted. Detailed specifications, technical deep-dives, reference architecture documentation, and integration walkthroughs are available under NDA for CTOs, CISOs, and enterprise security teams conducting formal evaluations.